Shadow AI: a serious risk factor
Shadow AI: a serious risk factor
Once upon a time, we had so-called “Shadow IT”: devices and software living outside IT’s control, used for convenience or just to bypass restrictions on corporate hardware.
I remember a consultant buddy working at a bank who told me, “*Since I can’t browse the web on the bank’s network, I just tether my phone. That way, I’m connected to the bank ****and ***the internet.” Absolute nightmare… It really makes you think: “It’s safer to just give them internet access than to have people using tricks like that.”
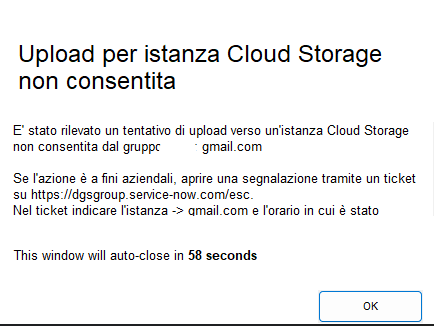
Today, restrictions are tighter than ever. We’ve got DLP (Data Loss Prevention) agents on endpoints blocking me from uploading perfectly legitimate, harmless personal docs to my *Google *or Proton Drive.
But now, there’s a new player in town: Shadow AI. There is virtually nothing stopping me from feeding highly confidential documents into free AI models (OpenAI, Google… probably *DeepSeek *or worse). We’re talking about sensitive info that threat actors would love to use to target my company or our clients.
It’s a serious issue. We’re burning cycles and budget blocking valid use cases, while AI is a massive, unmonitored security hole.