Huge Veeam logs directory in an Hardened Repo
Huge Veeam logs directory in an Hardened Repo
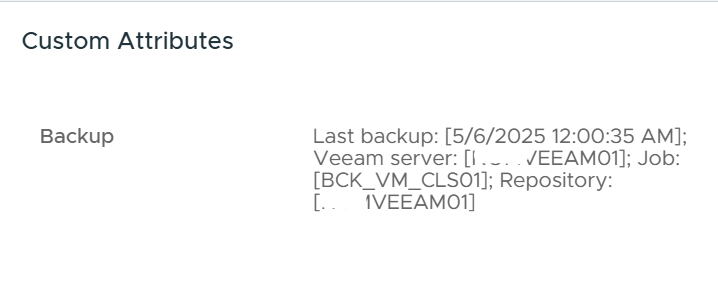
A customer with a very large Veeam environment using a Hardened Linux Repository pointed out that the /var/log/VeeamBackup directory was growing significantly — we’re talking tens of GBs.
On a Hardened Repo I have access to, I noticed quite a few fairly large log files, even though they were compressed. These files were owned by the non-root user that was used to connect the Linux server to Veeam.